SCADADome
SECURE AND SURVIVABLE CRITICAL INFRASTRUCTURE CYBER DEFENCE
SCADADome XDR Platform
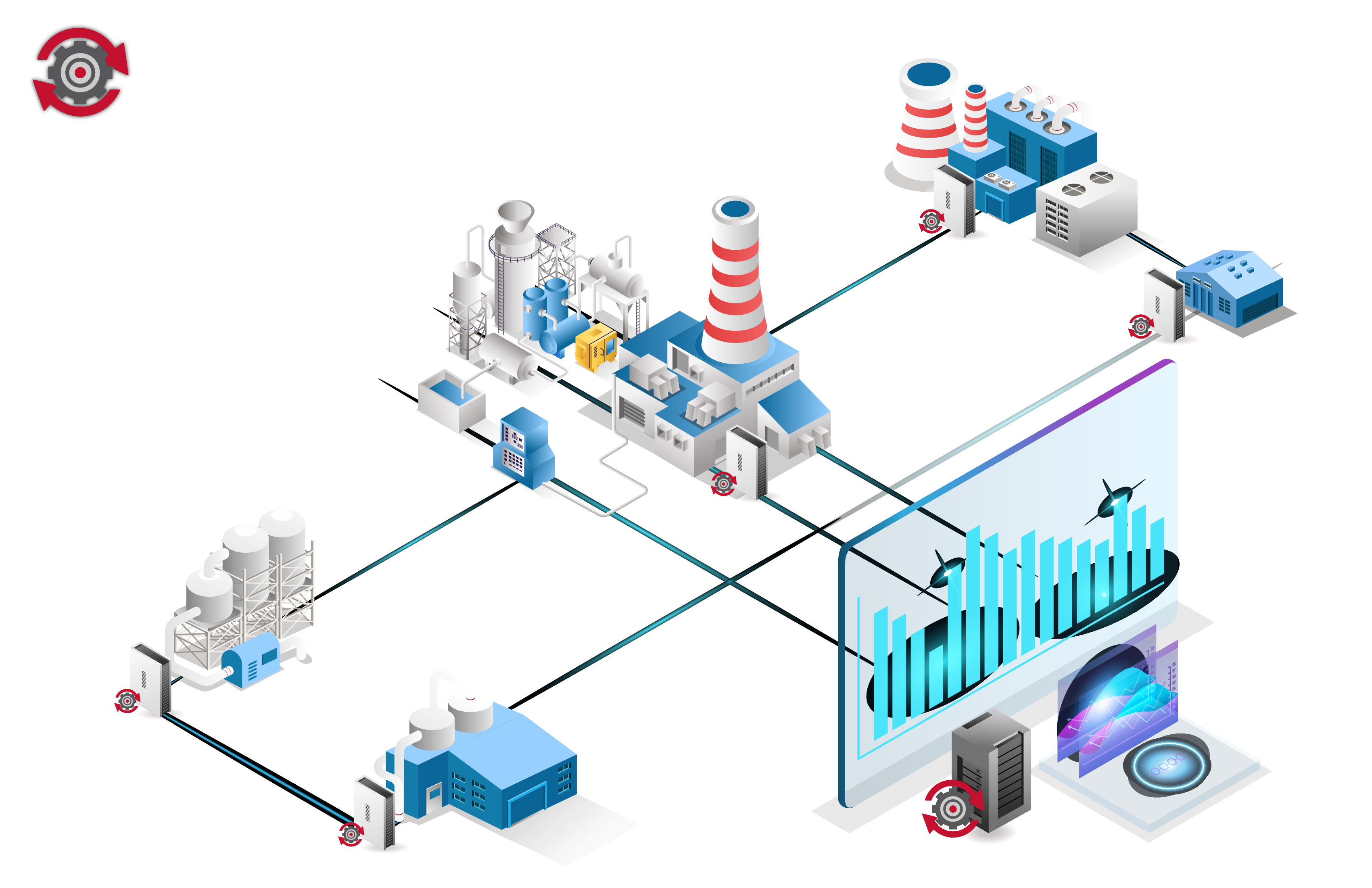
CRITIFENCE® SCADADome XDR Platform (SXP) is a new generation of cyber security technology which passively monitors and controls OT and IT networks through a server/agent architecture and enables remote site connectivity.
SCADADome XDR Platform (SXP) provides a multilayered defense ability designed to correlate between operation and security teams of the OT and IT networks, using different techniques such as machine-process learning, anomaly detection and hybrid data sources.
SCADADome XDR Platform (SXP) is designed to ensure a stable methodology which helps to protect Critical Infrastructure, IIoT, ICS and SCADA Systems. This approach consists of comprehensive cyber security principles:
- Visibility
- Detection
- Response
- Analysis
- Management






Oil & Gas
Water
Energy
Manufacturing
Wastewater
BMS
Chemicals
Nuclear
Communications
Transportation
Healthcare
Food & Agriculture



Contact
If you have any questions about SCADADome XDR Platform (SXP), please fill out the form below, and we will be in touch shortly.

Location:
65 Yigal Alon Street,
Tel Aviv, IL 6744316
Email:
sales@critifence.com
Phone:
+972 (73) 280 2266